Scan codebases to detect, classify and escalate cryptographic vulnerabilities.
Intelligent Scanning. Streamlined Remediation.
Designed for both today’s security challenges and tomorrow’s quantum era, Threat Point transforms cryptographic risk management into an adaptive, resilient capability.
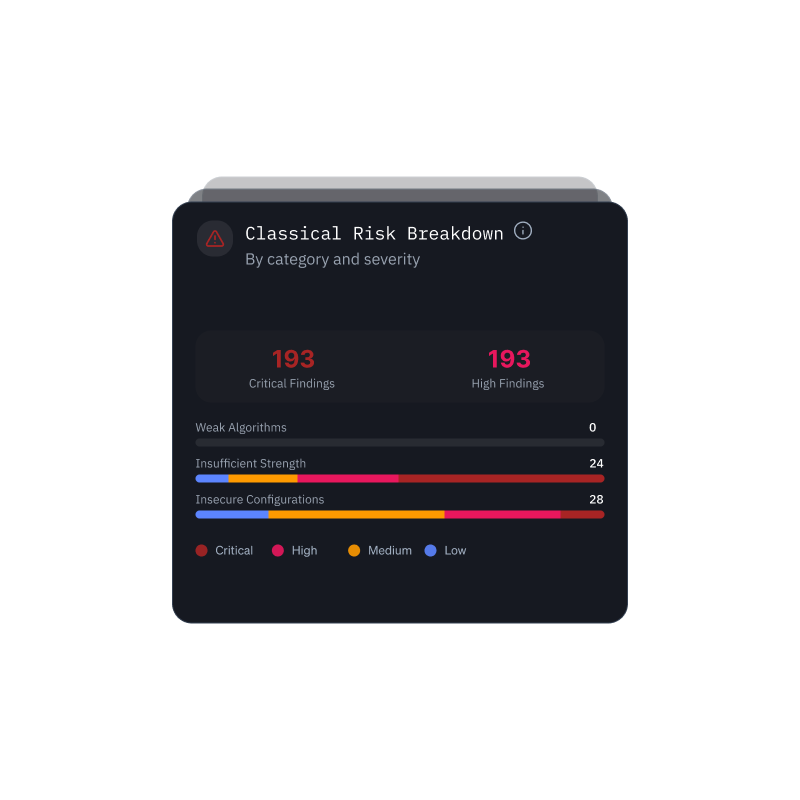
Cryptographic Vulnerabilities
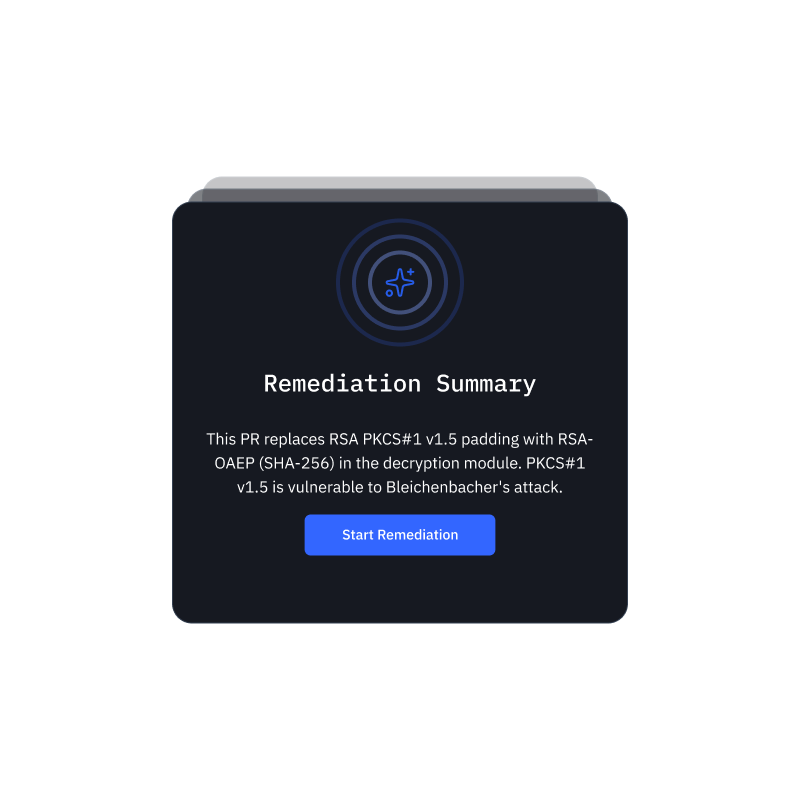
Streamlined Remediation
Automate remediation with AI-generated, contextual code fixes.
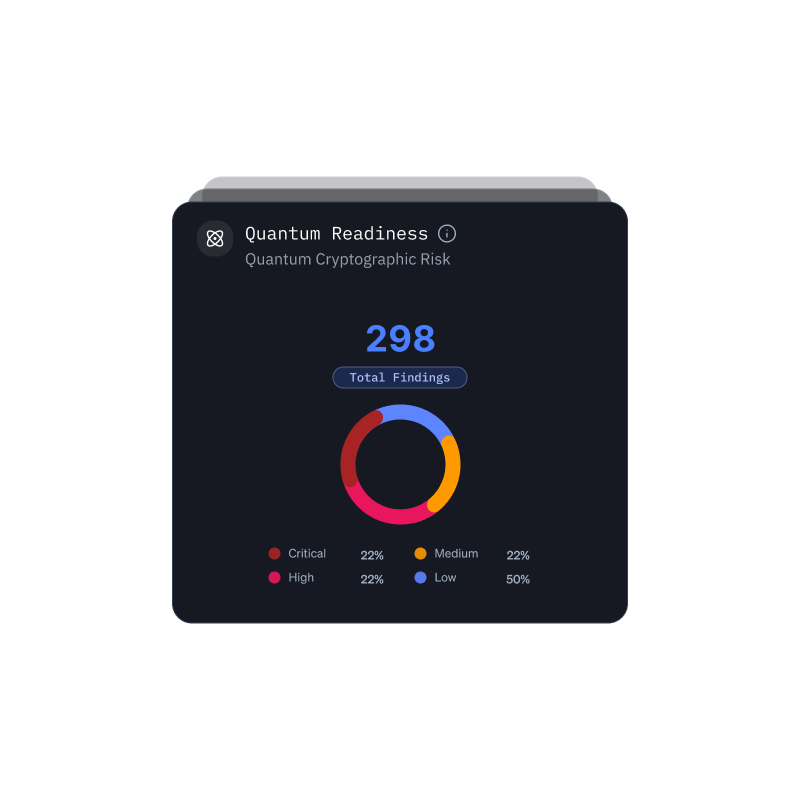
Quantum Readiness
Manage and track enterprise wide quantum safe cryptography.
Seamless Connection
Connect with Github for seamless workflows.